Key Takeaways
- Amazon says an unsophisticated threat actor used commercial AI services to compromise more than 600 FortiGate devices
- The campaign relied on exposed management ports and weak credentials rather than product vulnerabilities
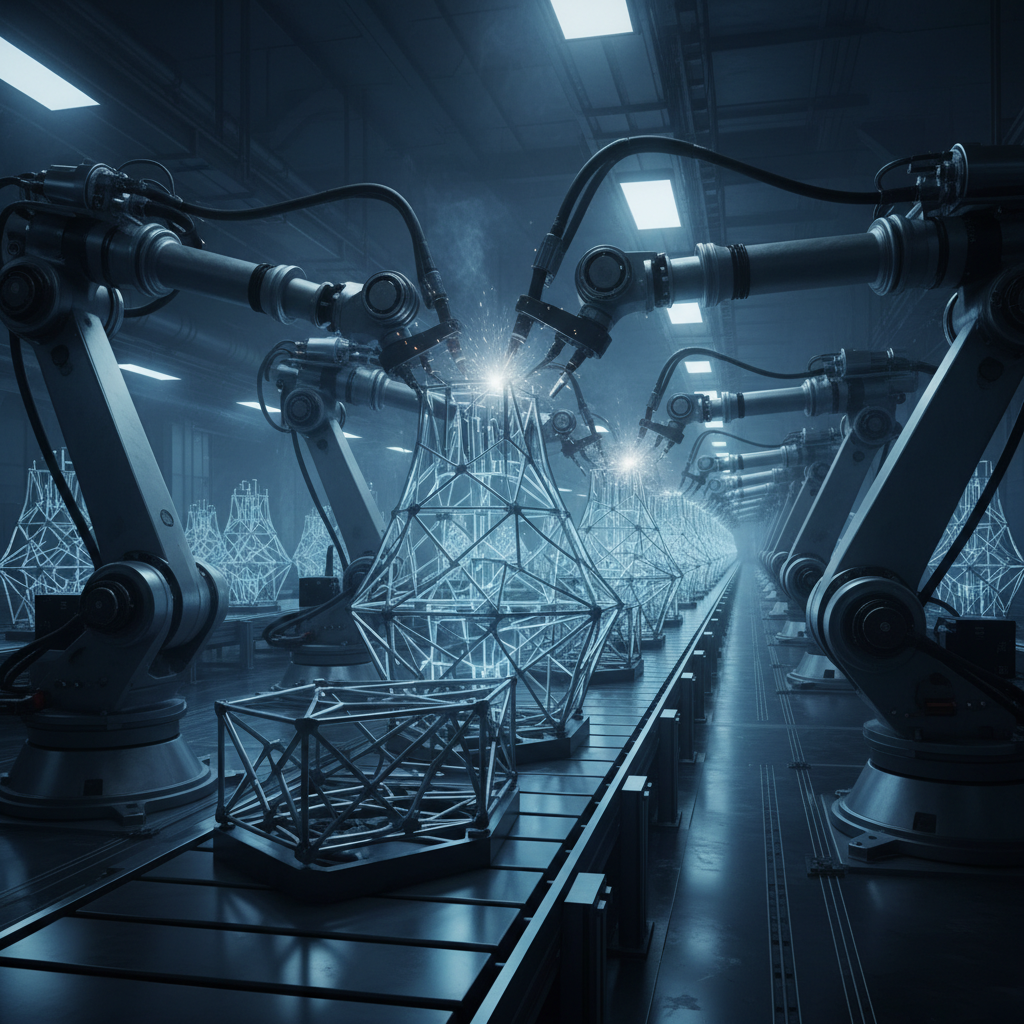
- Investigators found AI-generated tooling, plans, and configurations that resembled an assembly line for cybercrime
Amazon Threat Intelligence is drawing attention to a campaign that reflects a larger trend in security. A financially motivated, Russian-speaking threat actor leveraged commercial generative AI tools to carry out compromises across more than 600 FortiGate appliances globally. The activity was observed recently, and although the scale is significant, the technical methods were not particularly advanced.
What stands out is that no FortiGate vulnerability was exploited. Instead, the attacker focused on exposed management interfaces and weak, reused credentials that only required single-factor authentication. In other words, basic hygiene gaps enabled broad compromise. It is the kind of scenario security teams warn about repeatedly. Yet, here we are again, with fundamental misconfigurations driving risk.
The attacker used at least two commercial AI services to compensate for a lack of expertise. One service produced most of the operational planning, code scaffolding, and instructions. The second AI system was used when the actor needed to pivot inside certain networks. None of the services were named in Amazon’s report. Still, the pattern is familiar. Threat actors, especially those without deep technical skills, are increasingly turning to off-the-shelf AI systems because they simplify tasks that once required specialized talent.
Here’s the thing. It is not that AI magically grants them new offensive techniques. Both Amazon and recent work from Google’s security teams describe this shift the same way. AI accelerates mundane tasks and reduces trial and error. As a result, the ceiling on what a novice can accomplish rises. The barrier to entry for cybercrime keeps getting lower.
Amazon’s report notes that the attacker managed to compromise multiple Active Directory environments, extract full credential databases, and access backup infrastructure. Those steps often precede ransomware deployment. Yet, when the attacker encountered hardened environments, they simply walked away and focused on easier targets. It hints at the limits of automation. AI might help them move faster, but it does not replace hands-on skill when defenses are tight.
Investigators found publicly accessible infrastructure controlled by the attacker. It held AI-generated attack plans, victim-specific configurations, and code for custom reconnaissance tools. Amazon described the whole setup as resembling an assembly line for cybercrime. The metaphor is apt. When an actor can plug weaknesses into an automated workflow, they can reach dozens of organizations even without advanced capabilities.
At the core of the initial breach was systematic scanning of FortiGate management ports exposed to the internet. The attacker targeted ports 443, 8443, 10443, and 4443, then attempted authentication using commonly reused credentials. The scans were broad and sector-agnostic. All signs point to mass automation. According to Amazon, the activity came from a single IP address: 212.11.64[.]250.
Once inside, the intrusion path followed typical post-exploitation patterns. The actor performed reconnaissance using Nuclei, compromised Active Directory, harvested credentials, and sought access to Veeam backup infrastructure. Some of those steps involved known vulnerabilities such as CVE-2023-27532 and CVE-2024-40711. Versions of the attacker’s reconnaissance tool were written in Go and Python. The code analysis revealed several clues pointing to AI assistance, like redundant comments and simplistic architecture that valued formatting over engineering.
One question worth asking is whether organizations are ready for this kind of adversary at scale. Not because the techniques are new, but because the tooling becomes easier to reproduce. In effect, when a single individual or small group can act with the operational footprint of a much larger team, defenders feel the pressure.
There is another wrinkle. Amazon observed repeated failures whenever the attacker attempted more complex exploitation pathways. Their own notes referenced situations where services were patched, ports were closed, or no viable exploit existed. That pattern reinforces a long-standing defensive playbook. Routine patching, multi-factor authentication, and restricting administrative interfaces remain the strongest mitigations.
As expected, Amazon emphasized several best practices. Organizations should ensure management interfaces are not exposed to the internet. Common or default credentials must be changed and VPN accounts regularly rotated. Administrative and remote access should use multi-factor authentication. Backup servers should be isolated from general network access. Routine patching and careful monitoring for unusual exposure or unauthorized administrative connections are still fundamental.
The broader implication for businesses is that AI-augmented threat activity will continue to grow. Skilled and unskilled actors alike can use generative AI to scale known attack methods. Strong defensive fundamentals, especially on perimeter devices, remain the most reliable counterbalance.
 ⬇️
⬇️


