Key Takeaways
- Healthcare endpoint environments face increasing complexity and fragmentation that outpace traditional protection models
- Integrated approaches that combine data protection, cybersecurity, and backup tend to reduce operational burden
- Buyers evaluating endpoint protection platforms should look closely at automation depth, clinical workflow impact, and recovery capabilities
Definition and overview
Most healthcare organizations I have worked with over the years tend to reach a similar breaking point. They start with a reasonable set of endpoint tools, each chosen for a specific purpose. Then the environment shifts. A new clinical app, more remote diagnostics, an influx of mobile devices, tighter compliance requirements. Suddenly the tools no longer feel coordinated. The security team sees gaps. The IT team sees complexity. And clinical leadership starts asking why systems take longer to recover after disruptions. That tension is usually what sends providers back into the market for an endpoint protection management solution.
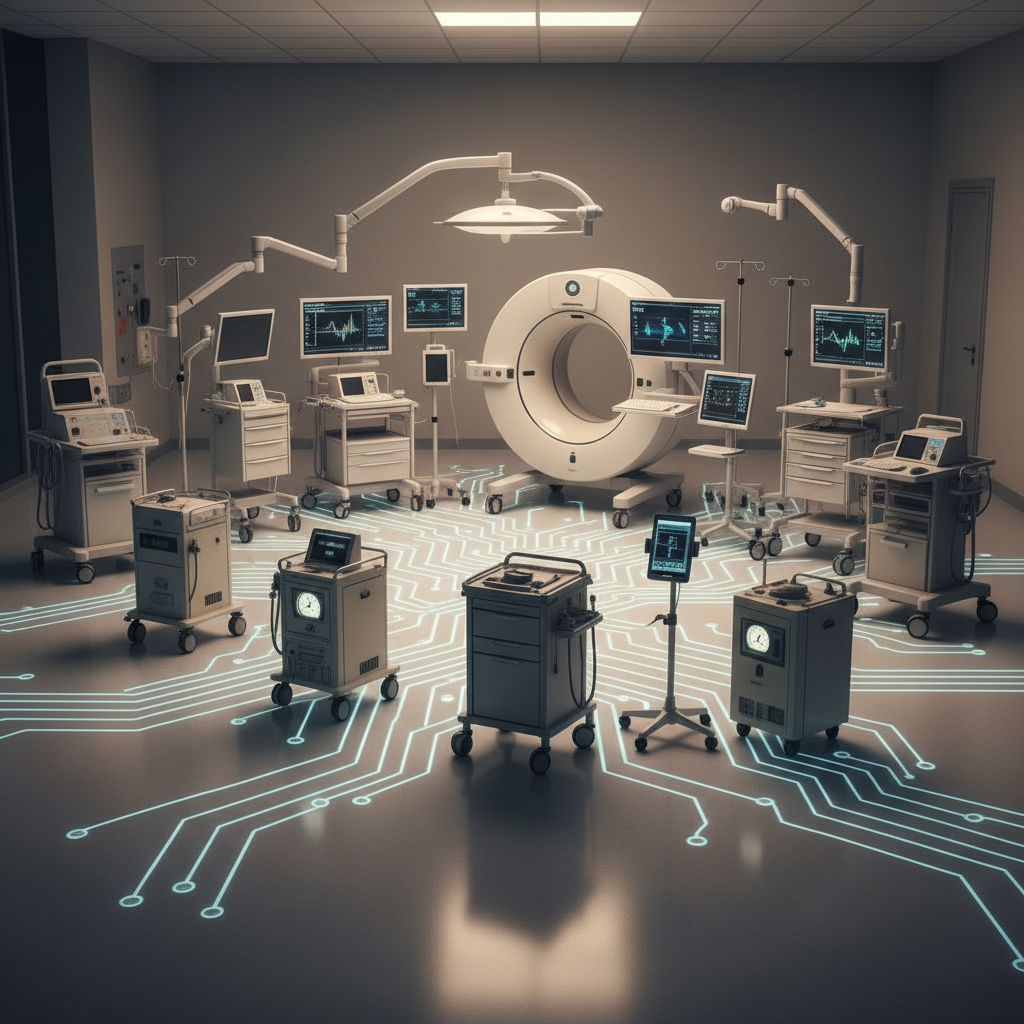
Endpoint protection management in healthcare refers to the coordinated controls that safeguard devices such as workstations, mobile carts, tablets, imaging systems, and remote clinician endpoints. It spans threat detection, hardening, monitoring, backup, and recovery. The concept is not new, though the stakes have changed. Healthcare has become one of the most targeted sectors for ransomware and data theft. At the same time, many legacy clinical devices cannot easily support modern security agents. This creates a patchwork that is difficult to manage at scale.
Within that context, platforms like Acronis have leaned into unifying data protection and cybersecurity in a single operational model. That idea has been floating around the industry for a decade, but only recently have the tools matured enough to make it realistic in day-to-day operations. Some IT leaders still wonder whether convergence reduces flexibility. Others find it is the only dependable way to move quickly without multiplying overhead.
Key components or features
Here is where things get interesting. Healthcare buyers often focus on malware prevention first, which makes sense, although endpoint protection in clinical environments tends to require a broader set of capabilities.
Common components include:
- Real-time threat detection and behavioral monitoring
- Centralized policy enforcement
- Secure backup and rapid restore
- Device health monitoring
- Vulnerability assessments and patch guidance
- Protections optimized for clinical devices that cannot be frequently updated
Even a basic inventory across a mid-sized provider shows how many device categories do not behave like standard corporate laptops. Ultrasound carts, lab analyzers, patient monitoring stations. Some run older operating systems. Some cannot be hardened using conventional methods. So the solution chosen must respect that reality instead of fighting it.
Integrated data protection features are becoming especially important. A question I hear often is: if a ransomware attack hits on a Saturday morning, how quickly can we recover clinical workstations without hunting through a maze of backup tools? The fastest restoring organizations usually rely on platforms that pair cybersecurity controls with embedded backup logic. A small detail maybe, but one that becomes a big deal during an outage.
Benefits and use cases
When comparing endpoint protection solutions for healthcare, three use cases tend to dominate the conversation.
The first is distributed care. Many providers now operate remote clinics or telehealth hubs that rely on secure endpoints outside the traditional network. These locations usually do not have local IT staff. So automation becomes essential, particularly for patching, malware response, and backup verification. A solution that needs hands-on tuning will struggle in this model.
The second is clinical system recovery. In practice, the speed of restoration has a direct effect on patient throughput. I once worked with a provider whose imaging devices took hours to restore after a security incident. The financial impact was immediate. Platforms that combine cybersecurity with backup workflows tend to shorten that window because they remove the friction between two formerly separate teams.
The third use case is compliance-driven oversight. Healthcare frameworks often require detailed reporting on device configuration, activity, and risk posture. Older endpoint tools rarely provide unified reporting across security, backup, and device health. A consolidated approach typically gives a clearer compliance narrative with fewer manual steps. That said, some organizations still prefer standalone tools, especially those with highly specialized security teams. It depends on culture and scale.
Selection criteria or considerations
Choosing between endpoint protection tools is not as simple as comparing feature grids. In healthcare, the operational context shapes the decision more than the marketing language.
Several considerations consistently surface:
- How gracefully does the platform handle legacy or semi-isolated clinical devices
- Does the solution reduce the number of consoles and agents IT must maintain
- What is the impact on clinician workflows, particularly during scans or software updates
- How fast can devices be restored after an incident, not only in theory but in daily practice
- Can the solution operate effectively across remote or bandwidth-constrained locations
Buyers often underestimate the importance of agent footprint and system resource consumption. Some clinical devices cannot tolerate performance hits from heavy security agents. Others cannot reboot frequently, which complicates update cycles. A balanced approach is key. Some endpoint protection suites offer lightweight modes or agentless options for sensitive equipment. Those small accommodations tend to make a large difference.
Another factor worth mentioning is the maturity of automation. Many providers lack the staffing to manually triage every security event. Solutions that automate repetitive tasks, such as isolating compromised endpoints or validating backup integrity, reduce operational load immediately. Platforms that integrate cybersecurity and backup also simplify one of the most overlooked steps, which is ensuring that recovery points are not infected. It sounds obvious, but it is a common failure point during real incidents.
Future outlook
The future of endpoint protection in healthcare feels like it is moving toward deeper convergence. Cybersecurity, data protection, and system recovery are becoming inseparable components of resilience. Providers want fewer silos, not more. They want tools that adapt to the unique rhythms of clinical environments instead of forcing a one-size-fits-all security model.
Emerging trends such as AI-guided threat analysis and automated remediation will likely shift expectations again. The challenge will be maintaining usability for healthcare teams who already operate under significant pressure. Some vendors are already aligning with this direction, though not all at the same pace. The organizations that find success usually choose platforms that simplify daily operations and shorten recovery times rather than chase every new feature.
Healthcare’s environment will keep evolving. New devices, more remote care, rising threat levels. Endpoint protection management must evolve with it, ideally with integrated approaches that reduce noise instead of adding to it.
 ⬇️
⬇️


