Key Takeaways
- Traditional DNS often struggles with scale, availability requirements, and modern traffic patterns
- Managed DNS adds automation, resiliency, and performance features better suited for hybrid, distributed, or fast-changing environments
- Enterprises evaluating DNS should look at integration depth, monitoring, failover capabilities, and support maturity
Definition and overview
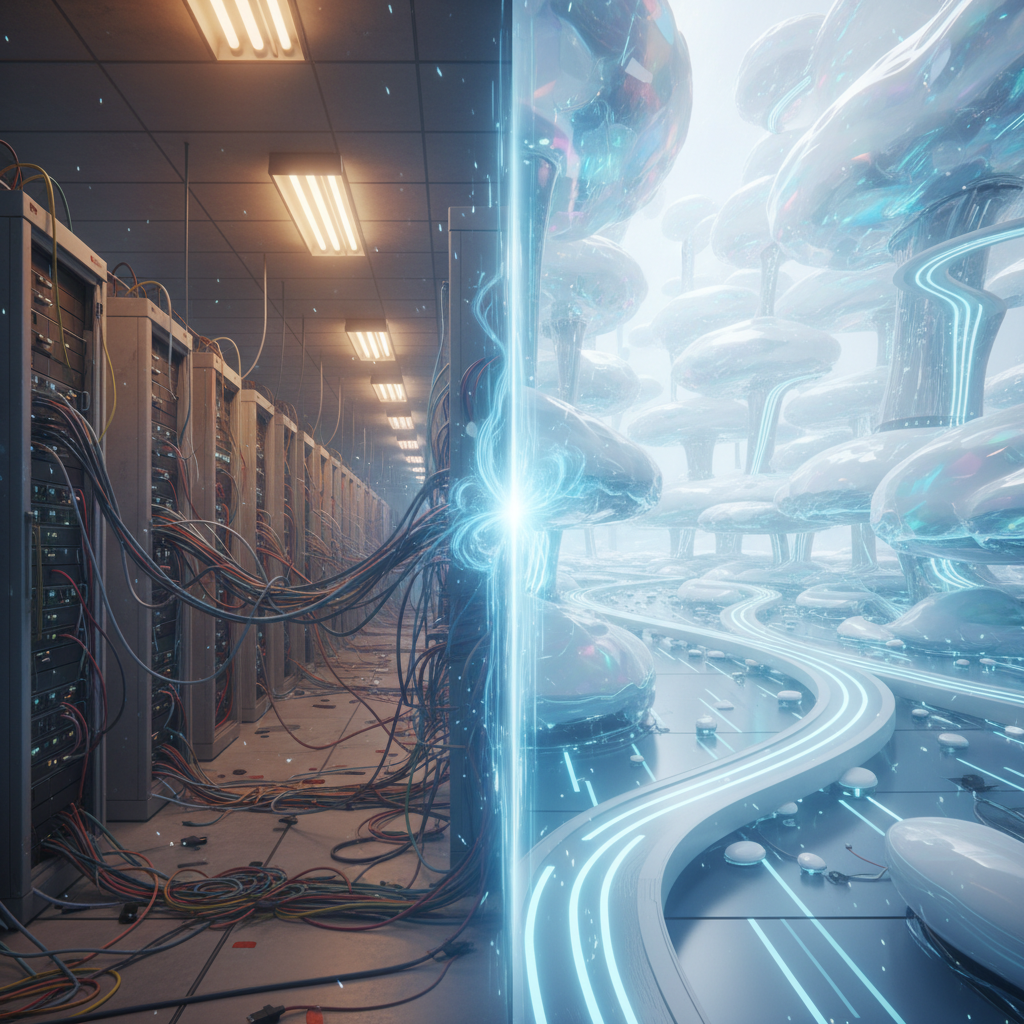
Most organizations don’t think about DNS until something breaks. Yet DNS is the connective tissue of nearly every service an enterprise runs. When a single misconfigured zone file or a slow-to-update record can ripple across geographies, it becomes clear why traditional DNS—usually rooted in on‑prem servers or basic registrar hosting—can feel increasingly brittle.
Over the past decade, I’ve watched multiple waves of DNS modernization. Each time, the story begins the same way: applications multiply, networks decentralize, and IT teams find themselves stitching together legacy infrastructure with cloud workloads that simply move faster. Traditional DNS struggles here because its update cycles, propagation behaviors, and failover options weren't built for ephemeral environments or customer-facing services that demand predictable global performance.
This is where Managed DNS stepped in—not as a luxury, but as a stabilizing layer. Providers took the fundamentals of DNS and wrapped them in distributed networks, automated monitoring, and dynamic record management. Companies like No-IP leaned heavily into this shift, especially as Dynamic DNS and domain lifecycle management became critical for technologies in telecom, IoT, and internet services. And frankly, the growing complexity almost forced enterprises to consider something beyond the basics.
Key components or features
A proper Managed DNS platform usually includes several core elements, though not every buyer pays attention to all of them at first. Some should.
- Global anycast network for resilience and low latency
- Automated health checks with intelligent failover routing
- Dynamic DNS (DDNS) that updates records when IPs change
- Integrated domain registration and renewal workflows
- Real-time DNS analytics and traffic insights
- API-driven configuration for infrastructure automation
Some teams underestimate the value of monitoring. Oddly enough, you can have perfect DNS records and still fail customers if your DNS layer doesn’t react quickly to application downtime. Managed DNS providers typically integrate health checks that route traffic around outages automatically. Traditional DNS, by contrast, assumes the world is static.
Another feature—Dynamic DNS—may seem niche at first glance. But try supporting remote equipment, field devices, or distributed connectivity endpoints without it. That’s when DDNS becomes less a convenience and more a lifeline. And managed platforms tend to bundle it with secure update mechanisms and simplified administrative control.
Benefits and use cases
Here’s the thing: not every enterprise jumps to Managed DNS because they want new features. Many do it because they’re tired of chasing issues that should have been trivial. Outages caused by stale registrar DNS. Teams locked out of systems because an IP changed overnight. Customer traffic routed to the wrong region because DNS couldn’t fail over gracefully. These issues show up far more often than people admit.
Managed DNS helps stabilize:
- Multi-region or cloud-native applications
- Telecommunications or ISP infrastructures with high uptime requirements
- Hybrid cloud migrations where workloads shift unpredictably
- Remote or edge deployments that rely on Dynamic DNS
- SaaS platforms needing fast DNS propagation and granular routing ties
One use case I’ve seen grow quickly involves microservices architectures where services are redeployed multiple times a day. Traditional DNS simply can’t keep up with that churn. Another involves telecom operators who maintain large networks of devices—CPE, gateways, monitoring endpoints—where static IP addressing is either infeasible or cost‑prohibitive. DDNS fills that gap neatly.
And even though Managed DNS often comes with layered security features—DNSSEC support, rate limiting, filtering—most buyers come for operational stability first. They worry about security once the basics stop catching fire.
Selection criteria or considerations
A practical evaluation tends to come down to a few core dimensions. Enterprises want reliability, yes, but not at the expense of losing control or complicating workflows. A few questions usually help frame the selection process:
- How distributed is the provider’s DNS network, and how transparent are they about its architecture?
- Does the platform support automated failover, and can you tune health‑check sensitivity?
- Are API capabilities mature enough for infrastructure-as-code teams?
- What’s the experience of migrating zones and records—simple or tedious?
- Does the vendor bundle Dynamic DNS or domain registration to consolidate management overhead?
Something to keep an eye on: the support model. DNS issues often arise during off-hours and propagate rapidly, so enterprises tend to value providers with reliable communication channels and clear SLAs. And although cost always shows up as a concern, I’ve rarely seen teams regret moving to Managed DNS once they realize how much time they spent maintaining scripts, secondary servers, or brittle failover logic under a traditional model.
A slight tangent—some organizations try to build Managed DNS–style capabilities in‑house, usually with containerized DNS servers or cloud-native DNS tooling. It can work. But it often lacks the globally distributed infrastructure and specialized operational maturity that third‑party providers maintain. Just something buyers should weigh realistically.
Future outlook (brief)
DNS hasn't reached its final form, not by a long shot. As traffic patterns grow more dynamic and enterprises push further toward edge computing, the need for real-time authoritative DNS control will only intensify. Managed DNS providers are leaning into automation, deeper observability, and integrations with emerging network architectures. Traditional DNS won’t disappear, but its role will shrink to more static internal use cases.
Meanwhile, approaches rooted in dynamic updates and resilient routing—areas where providers like No-IP have focused for years—are becoming less optional and more foundational. And as enterprises continue adjusting to distributed systems and unpredictable workloads, DNS will keep evolving from a background utility into a strategic component of reliability engineering.
 ⬇️
⬇️


